Data protection is vital in today’s society. Every technological improvement offers additional convenience and efficiency to our modern, comfortable lives. However, the ratio of improvement and the sacrifice of privacy keeps shifting. By captivating our attention and engagement with useful, irreplaceable, and addictive software, tech companies turn data collection into a profitable source of income. As modern businesses keep extracting and sharing private user information, the focus shifts on developing new, faster, silent, and secret ways to record, analyze and utilize our decisions, while the drive to create new revolutionary inventions require much more effort.
Turning users and customers into products is a much easier way to make money and pushing, and normalizing new, even inhumane methods of data collection gives much more power to tech companies. To counteract the absurdity of relentless information extraction, hiding location and IP address with a proxy is a good option that will protect you during browsing sessions, excluding the usage of social media networks. With a good provider, you can get residential IPs — the most secure addresses from real devices supplied by internet service providers. Be careful never to use free proxies because they are usually set up to steal data from unsuspecting internet users. Choose cheap datacenter proxies from a beginner-friendly provider, or residential IPs, mostly used for business-related tasks that depend on privacy and anonymity. Visit Smartproxy, a provider with great deals for all interested parties, to learn more about proxies and their role in digital privacy and data protection. Right now, let’s focus on the modern dangers that threaten online security and endanger our privacy.
Digital data protection tips

The internet has threats to user privacy, and they target different vulnerabilities. From immediate dangers from hackers and cybercriminals to slow, unsuspected drainage of data from tech companies, here we present a few tips that will help you protect private information.
Good password management
Password leaks are common cyberattacks that can spiral out of control. Using predictable symbol sequences or setting up the same passwords for all your accounts can have devastating effects.
For easy passwords, hackers and cybercriminals can even use algorithms that go through many accounts and test the most popular, easy-to-guess passwords. They find the most success with sequences that only have numbers and even codes made up strictly of numbers. Combinations of both letters and numbers are not bulletproof either. The strongest passwords have lowercase and uppercase letters, numbers, and at least one unique symbol. Even if you decide to use one password for all your accounts, better make it count! For good password management, massive threats are eliminated when all accounts have different passwords. However, having unique but strong sequences for each registration can be very hard to remember. If you want strong passwords but struggle to manage them, use password managers or browser extensions that will not only enter the correct passwords for each login but can also create new strong passwords for you.
Avoid unencrypted connections
Most popular websites use Hypertext Transfer Protocol Secure (HTTPS) instead of HTTP. HTTPS connections encrypt transmitted information to make sure no one can see the information in the data packets. Connecting to unprotected websites is unsafe, and you can give more data to potential cybercriminals.
Change your IP address
Without location tracking and social media accounts, your IP address and user agent are the main segments of private information used for profiling by tech companies. Also, if a malicious party or a potential hacker knows your IP address, they can slow down and disrupt your connection with DDoS attacks that overflow your network with connection requests.
Get yourself a proxy server to avoid exposing your IP address. With it, you can also change your access point and choose different geolocation, making you look like an internet user from that specific region. However, the further we go from our physical location, you will experience a proportionate drop in connection quality. If you want the best ratio of privacy and loss of internet speed, choose a proxy that will hide your approximate city prediction but is as close to your location as possible.
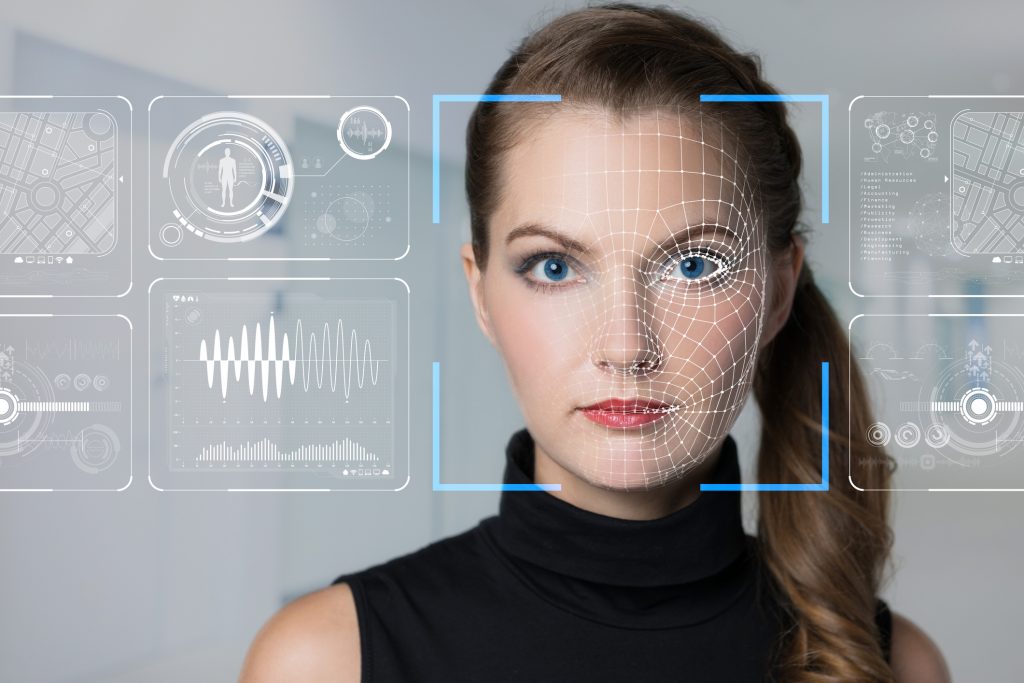
The threat of facial recognition
Facial recognition and AI are threatening people in China, and the same technologies are being used in western countries. When combined with GPS, IP location tracking, and digital footprints the user leaves on the web, the growth of facial recognition further intervenes with user privacy. Implementation of such technology can give too much power to the government, law enforcement, and tech companies. What may start as easy capture of criminals and unwanted persons may turn to unreasonable control of the population and exclusion, or even punishment to those who do not agree nor abide by the status quo. The combination of collected information allows the parties behind the technology to pinpoint your location and every decision at all times. If you are an internet user worried or even paranoid about your privacy, it may be the time to invest in a good baseball cap, a hoodie, or even facial reconstruction surgery to avoid being tracked at all times.








